FileMaker 16 Security Guide: Best Practices for Configuring Security Options
FileMaker security overview
About this guide
This guide describes the security features available with the FileMaker platform and the steps you can take as a solution developer, a server administrator, or an IT professional to apply these security features to your FileMaker solutions.
Depending on your security compliance and certification requirements, there may be additional steps you need to take. It is your responsibility to fully understand these requirements.
For the latest FileMaker security updates, see FileMaker Security Updates in the FileMaker Knowledge Base.
Note:This guide uses "Admin Console" to refer to both FileMaker Server Admin Console and FileMaker Cloud Admin Console, unless describing a particular product.
FileMaker security features
The FileMaker platform's features help you control data access, operations, and development within a FileMaker file. Key capabilities include:
- Authentication with accounts: FileMaker encrypts credentials stored within solutions so the credentials are protected. Users can also authenticate via Active Directory, Open Directory, or OAuth identity providers.
- Access control with privilege sets: You define permissions that determine levels of access to your solution. You can define as many privilege sets as needed.
- Data encryption on the disk and over the wire: You can encrypt the data stored within a FileMaker solution. You can also require Secure Socket Layer (SSL) encryption of data between FileMaker Server or FileMaker Cloud and FileMaker Pro, FileMaker Go, FileMaker WebDirect, and ODBC and JDBC client applications.
- Server monitoring and administration: Admin Console allows you to monitor solution access, disconnect idle users, and create backups of your solutions.
The FileMaker platform employs a unified security model, where the security that you establish for a solution is in effect across all clients.
Security settings defined within a solution using FileMaker Pro apply only to the information and schema (layouts, tables, fields, relationships, and scripts) stored in that solution.
Security settings configured within FileMaker Server and FileMaker Cloud are deployment specific and apply to all solutions hosted by the server.
System requirements
See the FileMaker Pro system requirements and the FileMaker Server system requirements.
Security for solution developers
Overview
Make the solutions you design in FileMaker Pro more secure by using FileMaker Pro features to authenticate users, limit access to the solution, encrypt data, and enhance functionality in secure ways.
Authenticate users
About authentication
FileMaker solutions require users to authenticate with an account name and password combination. Each account is given access privileges based on the associated privilege set. See Define privilege sets.
Create a unique account for each user. This allows you to track who is creating or modifying individual records or taking other actions in your solution. Track this information by using auto-enter field settings or by using the Get(AccountName) function in calculations and scripts. See Use functions, scripts, and script triggers to enhance security.
Note:Shared accounts are a security risk, so use individual accounts instead of shared accounts. If you must use shared accounts, limit the access capabilities of the privilege sets that the shared accounts use. Change the password frequently and when specific users no longer require access.
FileMaker solutions can authenticate accounts internally, externally, or with an OAuth identity provider.
- With internal authentication (via FileMaker Pro), the account name and password are stored within the solution. All security for a solution is set up in FileMaker Pro without server software, making it the quicker and easier option for managing accounts.
- With external authentication (via Open Directory or Active Directory) or with OAuth identity provider authentication, FileMaker Pro stores only user and group names and interacts with an external server or OAuth identity provider to authenticate a user's account and password. The solution must be hosted with FileMaker Server, and FileMaker Server must be configured to allow external authentication or individual OAuth identity providers. See Set up external authentication and Set up OAuth identity provider authentication.
About the default accounts
Each solution initially contains two accounts: Admin and Guest.
-
The Admin account permits access to everything in the solution. By default, this account is assigned the Full Access privilege set. This account is fully editable. You can rename it, assign it a password, and make the account inactive. You can delete the Admin account, but the file will require at least one account with the Full Access privilege set unless you remove that privilege set completely.
By default, the Admin account has no password. Assign a password when you first begin working in FileMaker Pro. See Assign the Admin account a password.
-
The Guest account allows users to access a file without supplying any account information. By default, this account is assigned the Read-Only Access privilege set, but you can assign the account any privilege.
Initially, the Guest account is inactive. You cannot delete the Guest account, change the Guest account name, or assign it a password.
Assign the Admin account a password
When you create a new solution, FileMaker Pro creates an Admin account with the Full Access privilege set. This Admin account does not have a password.
Be sure to assign a password to this account to prevent unauthorized access to your data and database schema.
See Creating and editing accounts in FileMaker Pro Help and Use strong passwords.
Disable the Guest account
When you create a new solution, FileMaker Pro creates a Guest account with the Read-Only Access privilege set. This Guest account does not have a password.
Do not enable the Guest account unless it is necessary for the solution. If you enable the Guest account, it's possible to quickly reach the maximum number of User Connections clients if many users log in to the Guest account in a short period of time.
See Creating and editing accounts in FileMaker Pro Help.
Create accounts
When you create an account, you give it an account name, password, and privilege set.
Select Require password change on next login in the Edit Account dialog box to prompt the user to create a password.
Passwords are stored using a one-way hash, meaning the password can be encrypted but never decrypted. You can reset a password, but you can't recover a password.
See Creating and editing accounts in FileMaker Pro Help and Use strong passwords.
Prompt users for a password
New solutions don't prompt for account names or passwords. To prompt users to enter account names and passwords, deselect Log in using in the File Options dialog box.
Do not allow Keychain Access to save account names and passwords. When you prevent Keychain Access, FileMaker prompts users to enter account names and passwords each time they open the solution. If you allow Keychain Access, you can require iOS users to enter their iOS device passcode before opening the solution.
See Setting file options in FileMaker Pro Help and Use strong passwords.
Set up external authentication
If you host files using FileMaker Server, you can create external server accounts that are authenticated by Active Directory or Open Directory. You can then use your existing authentication server to control access to databases, instead of managing an independent list of accounts in each FileMaker Pro database file.
Alternatively, you can use local security groups and accounts on the server machine hosting FileMaker Server. Refer to Help for your operating system.
Use external authentication if:
- your organization already uses Active Directory or Open Directory.
- your FileMaker file will be accessed by other files in a multifile solution.
- your organization enforces minimum password standards. FileMaker Pro can enforce elementary standards, such as password length and frequency of changing the password. External authentication offers more robust password control, such as enforcing password complexity requirements.
If you host files using FileMaker Server installed on Windows Server and use Active Directory for external authentication, your Windows users can use Single Sign-On with FileMaker Pro.
There is a risk with external authentication that someone will gain access to your file by simulating the external authentication environment or mismanaging the groups. It is your responsibility to prevent this by maintaining the security of your external authentication server. Enable database encryption for your solution files to reduce this risk. Database encryption requires users to provide the encryption password before they can share the file on FileMaker Server. See Encrypt data.
Set up external authentication accounts within the file using FileMaker Pro, then host the file using FileMaker Server and configure it for external authentication. See Creating accounts that authenticate via an external server in FileMaker Pro Help, Enable external authentication, and Setting up FileMaker Pro clients and FileMaker Server to use external authentication using the LDAP protocol in the FileMaker Knowledge Base.
Important information when using external authentication
- You must use the external authentication server to reset passwords.
- Set accounts in the order you want FileMaker to authenticate them. When multiple accounts share an account name and password, or when an external account belongs to multiple groups, FileMaker opens the file using the first matching account in the authentication order. Any matching accounts that follow the first are ignored.
- Do not create externally authenticated accounts with the Full Access privilege set. Maintain a local FileMaker account for administration purposes in case the file needs to be removed from FileMaker Server. If there are no local FileMaker accounts, FileMaker can open the file only if the file is hosted and the external authentication server is available.
Set up OAuth identity provider authentication
If you host files using FileMaker Server, you can create accounts that authenticate users via supported OAuth identity providers. This allows you to control access to your databases through third-party identity providers. This may also allow access to additional security measures—such as multifactor authentication, which requires more than one method of authentication. Instead of managing an independent list of accounts in each file, you can use your OAuth identity providers can control access to your FileMaker databases.
To authenticate via OAuth identity providers, use FileMaker Pro to set up accounts within the solution. Then host the solution using FileMaker Server, and configure FileMaker Server to authenticate with OAuth identity providers. See Creating accounts that authenticate via an OAuth identity provider in FileMaker Pro Help and Enable OAuth identity provider authentication.
Important information when using OAuth identity providers
- You must use the OAuth identity provider to reset passwords.
- Set accounts in the order you want FileMaker to authenticate them. When multiple accounts share an account name and password, FileMaker opens the file using the first matching account in the authentication order. Any matching accounts that follow the first are ignored.
- Do not create OAuth identity provider accounts with the Full Access privilege set. Maintain a local FileMaker account for administration purposes in case the file needs to be removed from FileMaker Server. If there are no local FileMaker accounts, FileMaker can open the file only if the file is hosted and the OAuth identity provider is available.
Authenticate in multifile solutions
FileMaker files can access one another in a multifile solution. This can be useful, for example, if you have a centrally accessible file of employee contact information that is used by multiple internal solutions.
When you open one file from another (such as for viewing external data or running a script in an external file), FileMaker passes the credentials the user supplied at login to the second file. If there is a corresponding account and matching password, FileMaker logs the user in to the second file. If there is no corresponding account, the user must log in to the second file.
You can create accounts manually in multiple files, but you may cause data entry errors. To reduce such errors, use external authentication. See Set up external authentication.
Review the accounts and privilege sets in each file of a multifile solution. If privilege sets do not match across files or an account has additional privileges in a file, users may gain access to data that would normally be restricted to them. See Define privilege sets.
Additionally, make sure that users cannot make references to files in a solution without the solution designer's assistance. Otherwise, they may gain access to restricted data. See Restrict references to a solution.
Define privilege sets
About privilege sets
Privilege sets grant access to the features a user can see and the tasks a user can do. They allow you to control access to data and schema. You can use a privilege set with multiple accounts.
Every new FileMaker solution contains three predefined privilege sets:
- Full Access: Allows complete access to the file, including all development features.
- Data Entry Only: Allows creating, editing and deleting records, and importing and exporting data. Does not allow access to any development features.
- Read-Only Access: Allows viewing and exporting record data. Does not allow modifications to the file except for values in global fields.
You can also create new privilege sets to meet your specific requirements. Typically, you will create a privilege set for each unique role in your organization. A privilege set is made up of these access options:
- Data access and design privileges: Provide access to a wide range of security control, including records, layouts, value lists, and scripts.
- Extended privileges: Determine how users access a shared file.
- Other privileges: Allow printing, exporting, and some other functions.
All clients and tools that access FileMaker solutions respect users' privilege sets. For example, if a user is assigned a privilege set that does not allow access to a field, the user cannot access the field via FileMaker Pro, FileMaker Go, FileMaker WebDirect, Custom Web Publishing, ODBC and JDBC applications, external tools like AppleScript or ActiveX, or by other means.
Create privilege sets
To create a privilege set, name and configure the privileges you want users to have for the solution.
By default, most privileges are turned off. This limits a user's privileges to only those necessary to fulfill the user's role.
See Creating and editing privilege sets in FileMaker Pro Help.
Define data access and design privileges
Data access and design privileges grant access to different parts of a file and apply to all tables, layouts, value lists, and scripts.
You can also design custom privileges to further restrict access privileges.
- Design custom privileges for records in order to control user access to individual tables or records. For example, you may have a CRM system where the sales managers can see all the records but individual sales representatives see only the records of their own customers and prospects.
- Design custom privileges for layouts to control whether and how users can view or modify a layout, and whether they can view or modify records when working with that layout. The FileMaker platform always uses the most secure combination of access rules. For example, a user who can generally edit records will be prevented from editing records on a layout that doesn't allow those privileges.
- Design custom privileges to control whether users can view, run, modify, delete, or create individual value lists and scripts.
See Editing record access privileges, Editing layouts privileges, Editing value list privileges, and Editing scripts privileges in FileMaker Pro Help.
Define extended privileges
Extended privileges determine how users access a shared file. Once you enable extended privileges for a privilege set, any accounts attached to that privilege set can access the file according to what the extended privilege allows.
The following table lists the default extended privileges.
| Keyword | Allows accounts to |
|---|---|
| fmwebdirect | Access a database file from a web browser via FileMaker WebDirect. |
| fmxdbc | Access a database file as an ODBC or JDBC data source. |
| fmapp | Open a shared file (either a file shared by FileMaker Pro or hosted and shared by FileMaker Server or FileMaker Cloud). |
| fmreauthenticate[x] | Access a file in FileMaker Pro or FileMaker Go without having to re-log in after file hibernation or after using a different app. The default time is ten minutes. |
| fmxml | Access a database file from a web browser or other application via XML web publishing (FileMaker Server only). |
| fmphp | Access a database file from a web browser or other application via PHP web publishing (FileMaker Server only). |
| fmrest | Access a database file from a web service via the FileMaker Data API (FileMaker Server only). |
| fmextscriptaccess | Access a database file from another application via Apple events and ActiveX. |
| fmurlscript | Perform a script from a URL. |
Important:If your users use FileMaker Go, specify the fmreauthenticate[x] extended privilege.
FileMaker Go allows multitasking. When the user answers a call or moves to another app, FileMaker Go moves to the background and saves the state of the file.
With the fmreauthenticate[x] extended privilege, when FileMaker Go switches to the foreground, users must reenter the account name and password if the specified time limit, [x] minutes, has elapsed. For example, an extended privilege of fmreauthenticate10 allows the user to keep FileMaker Go in the background for up to ten minutes before the user must log in again. You can create as many extended privileges with different time periods as you need and assign them to different privilege sets. Users can attempt to enter their account name and password five times before FileMaker Go closes the file. Set [x] to 0 to make users log in any time FileMaker Go returns to the foreground.
The fmreauthenticate[x] extended privilege also reconnects a FileMaker Pro or FileMaker Go client to a FileMaker host after a network outage or a standby server switchover operation. If the client was disconnected from the host for over x minutes, the client must reauthenticate.
You can create custom extended privileges to simplify your scripts or to manage the business rules you need to enforce. For example, create custom extended privileges to allow users to run certain reports.
See Editing extended privileges for a privilege set in FileMaker Pro Help.
Define other privileges
Other privileges specify whether the privilege set allows users to:
- print – includes both printing and saving records as PDF
- export – includes exporting records, saving records as an Excel file, copying records in a found set to the Clipboard, saving a copy of the file, accessing data with Apple events, and using the file as the source of an import
Note:This privilege doesn't affect accessing data with ActiveX. - manage extended privileges
- override data validation warnings
- disconnect users from a hosted solution when a client is idle
- modify their passwords
- access menu commands (all, editing only, minimum)
See Editing other privileges in FileMaker Pro Help and Disconnect idle users.
Remove the Full Access privilege set
To ensure that users can't gain access to parts of the solution and schema that would normally be restricted to them, use FileMaker Pro Advanced to permanently remove the Full Access privilege set from the solution.
Important:Removing the Full Access privilege set permanently deletes from the solution all accounts that were using the Full Access privilege set. This permanently eliminates access to Layout mode, the Script Workspace, and all tabs in the Manage Security dialog box except Extended Privileges. This includes all database files in the solution, whether opened in a runtime application or in FileMaker Pro or FileMaker Pro Advanced. Schema and design elements of the files cannot be recovered. The only way to modify the tables, field definitions, relationships, scripts, or access privileges is by returning to the original file before it was customized by the Developer Utilities in FileMaker Pro Advanced.
See Removing Admin access to databases (FileMaker Pro Advanced) in FileMaker Pro Help.
Encrypt data
Encrypt a solution
Use FileMaker Pro Advanced to encrypt all the information stored in a file (also known as Encryption at Rest). Database encryption protects your solution if someone gains physical access to the file.
Database encryption requires a local FileMaker account with Full Access privileges to all files, an encryption password, and a shared ID. Users must enter the encryption password whenever FileMaker Pro or FileMaker Go opens a local file, or when FileMaker Server or FileMaker Cloud opens a file before hosting it. The shared ID links multiple encrypted files. When one encrypted file attempts to access another encrypted file, the user will not be prompted again for the encryption password if the files' encryption passwords and shared IDs match.
See Encrypting database files (FileMaker Pro Advanced) in FileMaker Pro Help and Use strong passwords.
When you open an encrypted file on FileMaker Server or FileMaker Cloud, you can save the password to automatically open encrypted files when the server restarts. FileMaker employs a two-way AES-256 encryption that uses a composite key based on information from the machine to encrypt the password and stores the password securely on the server.
See Opening hosted files and Clearing the database encryption password in FileMaker Server Help, and Encrypting and uploading database files in FileMaker Cloud Help.
Encrypt field data
Use the CryptEncrypt, CryptEncryptBase64, CryptDecrypt, and CryptDecryptBase64 functions to encrypt and decrypt field data within a FileMaker solution.
Encrypt container data
If database encryption is enabled for a solution, or if container data is configured to be stored externally, all container data is encrypted by default. If you don't want to encrypt container data when you encrypt database files or store container data externally, you can keep the container data in open storage. See Encrypting database files (FileMaker Pro Advanced) and Setting up container fields to store data externally in FileMaker Pro Help.
Limit access to the solution through layouts
Design layouts that limit users' view of data and access to features according to their needs and privilege sets. Also, consider hiding the status toolbar and instead providing buttons that perform allowed tasks.
If the solution will be used with FileMaker WebDirect or FileMaker Go, design layouts for express use with these clients. See FileMaker WebDirect Guide and FileMaker Go Development Guide.
Note:Limiting access to solution data and features on a layout does not prevent users from accessing data with script steps, functions, AppleScript, or by other means. Define privilege sets to restrict user access to data and features in all clients. See Define privilege sets.
Use functions, scripts, and script triggers to enhance security
Use FileMaker functions, scripts, and script triggers to enhance security for common tasks such as deleting, auditing, and maintaining records. For example, use scripts to:
- add or delete accounts, reset account passwords, change passwords, enable or disable accounts, and re-log in as a different user
- archive records when you don't want a user to delete records
- provide information about the user's current session and state for regulatory compliance and auditing
- provide custom messages when security limitations affect the user
Important:Do not use functions, scripts, or script triggers to replace FileMaker security features.
Keep the following points in mind:
- By default, scripts run using the privilege set of the account that is currently logged in. This can cause issues if the script tries to perform an action the user does not have the privileges to do. Test all scripts across all privilege sets to protect the integrity of your data.
- When using script steps to communicate with systems outside FileMaker, choose available options that interact via SSL encryption. For example, the Insert from URL script step includes the Verify SSL Certificates option, and the Send Mail script step allows communication with SMTP servers that use SSL encryption.
- Use functions to get information about the current user. For example, use the Get(AccountExtendedPrivileges) function to test whether a user has a specific privilege.
See Functions reference, Script steps reference, and Script triggers reference in FileMaker Pro Help.
Restrict references to a solution
Restrict references to a solution to prevent the solution's schema from being accessed by unauthorized files. For another file to access the solution's schema and data, either the file must be authorized within the solution or the user must enter valid credentials for the solution.
You can specify that only accounts with the Full Access privilege set can create references to the solution, ensuring that only solution designers and administrators can reference the solution.
In a multifile solution, you must authorize each file that needs access to another file's schema.
See Authorizing access to files in FileMaker Pro Help.
Set a minimum client version
Set a minimum version of FileMaker Pro or FileMaker Go that's allowed to access the solution. Newer versions of FileMaker clients provide features and security changes not available in older versions, so restrict which clients can access to the solution. See Setting file options in FileMaker Pro Help.
Enable plug-ins
Use plug-ins only from trusted sources, because plug-ins can access and modify your solution and connect to other services over the Internet.
For additional security and to prevent unauthorized plug-ins from being installed, you can enable or disable the installation of plug-in files. This is a FileMaker Pro preference, not a file preference, and determines whether plug-ins can be installed on the user's computer.
See Setting plug-in preferences in FileMaker Pro Help. To enable plug-ins in FileMaker Server, see Enable plug-ins in FileMaker Server and FileMaker Cloud.
Security for server administrators
Overview
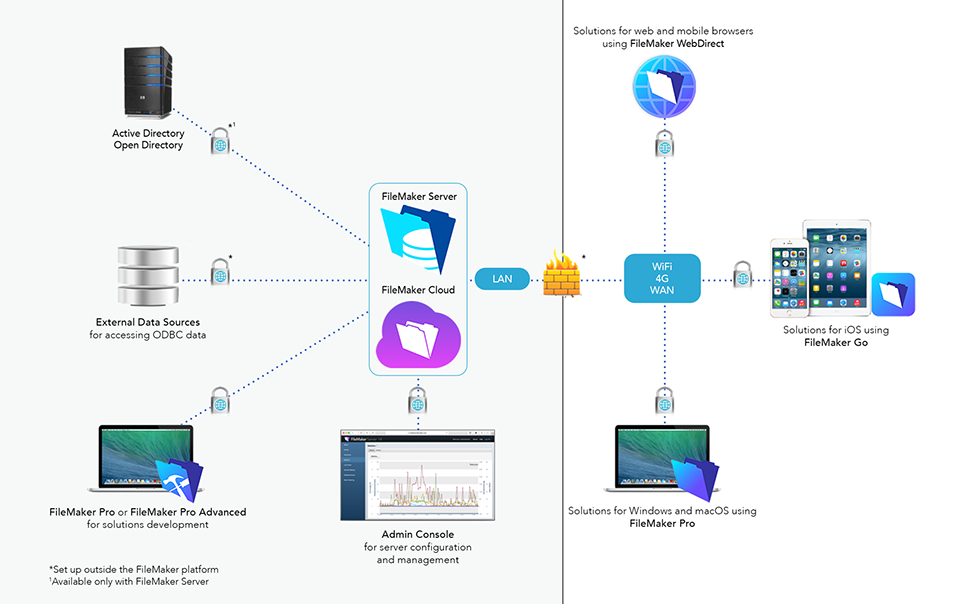
FileMaker Server and FileMaker Cloud host solutions for the following clients:
- FileMaker Pro
- FileMaker Go
- FileMaker WebDirect
- Web users and web applications via the Web Publishing Engine (FileMaker Server only)
- ODBC and JDBC applications
The following sections outline the steps for setting up security in FileMaker Server and FileMaker Cloud.
If you are using FileMaker Server, be sure that you installed it in a secure location and that you are using SSL encryption to encrypt HTTPS communication between clients and the server:
Enable external authentication
Note:This feature is not available in FileMaker Cloud.
With FileMaker Server, you can use your existing authentication server to control access to files without having to manage an independent list of accounts in each file.
Set up external authentication accounts within the file using FileMaker Pro, host the file using FileMaker Server, and configure it for external authentication. To set up accounts in FileMaker Pro, see Set up external authentication.
To enable external authentication in FileMaker Server:
- In FileMaker Server Admin Console, choose the Database Server > Security tab.
- Select FileMaker and external server accounts in the Client Authentication section.
To use Active Directory or Open Directory, the server where FileMaker Server is installed must be a member of the domain used for external authentication.
Test thoroughly. See Test security settings.
Enable OAuth identity provider authentication
With FileMaker Server, you can use supported OAuth identity providers to control access to files without having to manage an independent list of accounts in each file.
Set up OAuth identity provider accounts within the file using FileMaker Pro, host the file using FileMaker Server, and configure it for OAuth identity provider authentication. To set up accounts in FileMaker Pro, see Set up OAuth identity provider authentication.
To enable OAuth identity provider authentication in FileMaker Server:
- In FileMaker Server Admin Console, choose the Database Server > Security tab.
- Select FileMaker and external server accounts in the Client Authentication section.
- Click
 for the OAuth identity provider that you want to set up. Follow the instructions in the dialog box that opens, and click Save to enable the OAuth identity provider.
for the OAuth identity provider that you want to set up. Follow the instructions in the dialog box that opens, and click Save to enable the OAuth identity provider. - Stop and restart the FileMaker Server service (Windows) or FileMaker Server background processes (macOS).
To enable OAuth identity provider authentication in FileMaker Cloud, see Setting up client authentication in FileMaker Cloud Help.
Test thoroughly. See Test security settings.
Limit the list of hosted solutions
Note:This feature is not available in FileMaker Cloud.
The Launch Center in FileMaker Pro, FileMaker Go, and FileMaker WebDirect displays a list of hosted solutions. By default, the list shows all the hosted solutions available on a server. With FileMaker Server, you can limit this list to show only the solutions that the current user may access. See Database Server security settings in FileMaker Server Help.
Require passwords for hosted files
Make sure all hosted databases require a client to specify an account and password. The following types of databases are insecure:
- databases that have a Guest account using the Full Access privilege set
- databases that have any Full Access account with an empty password
- databases that have any Full Access account with the password stored in the database (using the FileMaker Pro File Options dialog box Log in Using option)
By default, FileMaker Server prevents insecure databases from being hosted. See Database Server security settings in FileMaker Server Help. FileMaker Cloud always requires password protection for hosted databases.
When a FileMaker Pro user attempts to upload a database using the Upload to FileMaker Server menu item, FileMaker Pro validates that the database is password protected. If the host requires databases to be password protected, FileMaker Pro doesn't allow the above types of insecure databases to be uploaded.
View log files
As FileMaker Server and FileMaker Cloud run, they log server activity. Use the log files to collect client access information and other information needed for regulatory and auditing purposes.
To view logs and log file entries, see Viewing log file entries in FileMaker Server Help and Downloading software and logs in FileMaker Cloud Help.
Disconnect idle users
Set the maximum amount of time that FileMaker users can be idle when they are connected to a file hosted by FileMaker Server or FileMaker Cloud. This idle time limit reduces the risk of your files being accessed by an unattended computer or mobile device. However, make sure the idle time is long enough to avoid frequent disconnections.
In FileMaker Pro, in the Edit Privilege Set dialog box, select Disconnect user from server when idle for each privilege set you want disconnected when a user is idle. Because you can set this option for each privilege set, certain users are disconnected when idle and other users will always maintain their connections. In FileMaker Pro and FileMaker Go, users logged in with the Full Access privilege set are never disconnected when idle.
To specify the idle time, see FileMaker clients settings in FileMaker Server Help and Setting session timeouts in FileMaker Cloud Help.
Set up backups
It's important to back up FileMaker solutions to prevent data loss. If data in a file is destroyed, you can revert to the backup.
Backups in FileMaker Server
FileMaker Server offers two types of backups: scheduled and progressive. Be sure to specify a secure physical location for stored backups.
With a scheduled backup, FileMaker Server checks whether data has changed since the last backup and creates a full copy of any databases and container data that have changed.
With a progressive backup, FileMaker Server creates two full backups in the progressive backup folder of all hosted databases. Then, after the specified interval, it applies any changes to the oldest backup copy.
FileMaker Server saves backups only to local disks. Use other tools to copy the local backups to provide offsite backups for disaster recovery.
Important:FileMaker Server creates the directory structure for these backups. To work with a backup file, leave the original file unchanged in the backup folder. Never open the original backup file with FileMaker Pro, edit it, or move it out of the backup folder. Instead, copy the file and work exclusively with the copy.
See Understanding backup options in FileMaker Server Help.
Backups in FileMaker Cloud
FileMaker Cloud offers backups as snapshots of your storage volume, which contains all your data, including databases, configurations, and logs. Backups run every twenty minutes, and FileMaker Cloud stores one week of backups.
See Working with backups in FileMaker Cloud Help.
Add administrators
Administrator groups in FileMaker Server
As the server administrator, you can use administrator groups to delegate database administration tasks to other users. You retain exclusive and complete control of FileMaker Server. Group administrators are not allowed to configure FileMaker Server, and you specify which database administration tasks the group administrators may do.
You can use external authentication to validate the credentials of the users in your administrator groups and to support Admin Console login. See Enable external authentication.
See Configuring administrator group settings in FileMaker Server Help.
Non-root administrators in FileMaker Cloud
As the root administrator, you can allow non-root administrators to log in to FileMaker Cloud and manage most aspects of the FileMaker Cloud instance. Non-root administrators can't modify other administrator accounts, import SSL certificates, or discontinue the FileMaker Cloud subscription.
See Adding an authenticated user to FileMaker Cloud in FileMaker Cloud Help.
Decide whether to permit the Perform Script on Server script step
Note:This feature is not available in FileMaker Cloud.
For performance reasons, solution developers may design FileMaker Pro databases to use the Perform Script on Server script step. For security reasons, FileMaker Server administrators can decide whether to permit Perform Script on Server in hosted solutions.
To disable use of Perform Script on Server, use the FileMaker Server Admin Console Database Server > FileMaker Clients tab to set the Maximum Simultaneous Script Sessions to 0 (zero). Any value above zero will allow the Perform Script on Server script step to perform in hosted solutions.
See FileMaker clients settings in FileMaker Server Help.
Enable plug-ins in FileMaker Server and FileMaker Cloud
Solution developers can design FileMaker Pro databases to use server-side plug-ins. To enable plug-ins in FileMaker Pro, see Enable plug-ins.
Enable FileMaker Script Engine (FMSE) plug-ins and Web Publishing Engine (WPE) plug-ins in Admin Console. This setting enables the FileMaker Script Engine to use external function plug-ins.
In FileMaker Server Admin Console, you can allow scheduled scripts and scripts that run using the Perform Script on Server script step to install, update, and load plug-ins by selecting the Allow Install Plug-In File script step to install, update, and load Server plug-ins setting in the Database Server > Server Plug-Ins tab. If some plug-ins may be a security risk, leave this checkbox deselected. When this checkbox is deselected, you can still manually install plug-ins on the server, then use the Database Server > Server Plug-Ins tab to enable or disable the plug-ins.
In FileMaker Cloud, you can install plug-ins with the Install Plug-in File script step.
See Server plug-in settings in FileMaker Server Help and Managing server plug-ins in FileMaker Cloud Help.
Ensure email notifications are secure
In FileMaker Server Admin Console, if you use the General Settings > Email Notifications tab to enter the SMTP configuration information for an email server, verify the security of that email server. The email server should always use the most recent Transport Layer Security (TLS) protocol for communication.
See Email notification settings in FileMaker Server Help.
Note:Emails sent from FileMaker Cloud Admin Console always use TLS.
Security for IT professionals
Overview
FileMaker software runs on your computers and your network. Clients may be accessing your hosted data using your company intranet or over the Internet. As you consider the security of the FileMaker platform, consider the security of your system environment.
The following sections describe how to make your system environment more secure for the FileMaker platform.
Secure the machine running FileMaker Server
Though accounts and privilege sets provide good database protection, they do not provide a completely secure solution. If you're using FileMaker Server, you must protect access to your files and information, and not rely solely on FileMaker Pro access privileges. For example:
- Protect the physical security of the computers, hard drives, and backup storage media where the database files reside. For example, place the computer running FileMaker Server in a locked room.
- If you host FileMaker Pro databases on a computer that is shared over a network, use operating system security settings and passwords to restrict folder and file access to authorized personnel.
- Set the screen saver feature of your operating system to require a password in order to wake up the computer.
- Never run other network services, such as an email server, on the same machine as FileMaker Server.
- Verify that all other network services support only the highest level of security possible—for example, the most recent TLS protocol. These network services should disable support for insecure protocols—for example, SSLv2 and SSLv3.
Install FileMaker Server components behind the firewall
FileMaker Server contains up to three components:
- Database Server
- Web Publishing Engine
- Web Server Module
You deploy these components on the master machine and can add additional Web Publishing Engines and Web Server Modules on worker machines. You can control where each machine is in relation to your firewall. For example, you can choose to place all components behind the firewall to restrict access to the LAN network. If you place any machines in your deployment behind the firewall, you must open the ports used by FileMaker WebDirect in the firewall to make FileMaker WebDirect available over the Internet. See Ports used by FileMaker Server.
Important:To enhance the security of your database solution, especially over the Internet, use a firewall on the public side of a FileMaker Server deployment, and use SSL for the web server. See Set up SSL encryption.
See chapter 1 of FileMaker Server Installation and Configuration Guide.
Set up SSL encryption
Encrypt the data passed between FileMaker Server or FileMaker Cloud, FileMaker clients, and ODBC and JDBC applications by using SSL technology. An SSL certificate is a data file provided by a certificate authority (CA) that digitally identifies the sender, receiver, or both parties of a secure transaction. SSL certificates are installed on machines running FileMaker applications to provide secure connections between FileMaker Server or FileMaker Cloud and FileMaker clients.
SSL encryption is especially important if clients are accessing your hosted data over the Internet. If you do not use encryption, then your data may be viewed by software that is monitoring your network.
To enable SSL encryption, see Securing your data in FileMaker Server Help. SSL encryption is enabled by default in FileMaker Cloud.
Notes
- Never share the same SSL certificate between a FileMaker Server machine and a machine running less-secure network services—for example, an email server.
- Never use the same private key to generate multiple SSL certificates that are used on different machines—for example, a FileMaker Server and an email server. A successful attack on the email server could compromise all the other certificates that use the same private key.
- In a multiple-machine FileMaker Server deployment, use a Subject Alternative Name (SAN) certificate or a wildcard certificate on the master and worker machines. Otherwise, each machine in the deployment requires an SSL certificate that matches its unique hostname.
See List of supported SSL certificate types and vendors for FileMaker platform in the FileMaker Knowledge Base.
About the default certificate in FileMaker Server
FileMaker Server provides a default SSL certificate signed by FileMaker, Inc., that does not verify the server name.
Important:The FileMaker default certificate is intended only for test purposes. A custom SSL certificate is required for production use.
About the default certificate in FileMaker Cloud
FileMaker Cloud provides a default SSL certificate issued by the Comodo certificate authority (CA). You can renew the default certificate or import your own custom certificate. See Importing SSL certificates in FileMaker Cloud Help.
Enable HTTP Strict Transport Security
If FileMaker Server has a valid SSL certificate, HTTP Strict Transport Security (HSTS) restricts web clients to HTTPS connections. Once a web client connects to FileMaker Server via HTTPS with HSTS, the web browser prevents the client from using an HTTP connection for content hosted by FileMaker Server.
To enable HSTS in FileMaker Server, see Database Server security settings in FileMaker Server Help.
Note:HSTS is always enabled in FileMaker Cloud.
Test for SSL encryption
To test the encryption between the FileMaker Server or FileMaker Cloud and FileMaker Pro or FileMaker Go clients, use the Get(ConnectionState) function. It will return a value of:
- 0 for no network connection for the current file.
- 1 for a connection that is not encrypted (FileMaker Server with SSL disabled, or to a FileMaker Pro host).
- 2 for a connection that is encrypted but for which the SSL certificate for FileMaker Server cannot be verified. You may be connected to a server pretending to be your actual destination, which could put your confidential information at risk.
- 3 for a connection that is encrypted with a verified SSL certificate.
For example, write a script to run when a file is opened that alerts the user if the connection to FileMaker Server is not secure.
The user may see a lock icon in the FileMaker Pro Open Filename dialog box, the upper-right corner of the FileMaker Pro window, or the FileMaker Go Opening File screen.
 is equivalent to Get(ConnectionState) returning 1.
is equivalent to Get(ConnectionState) returning 1. is equivalent to Get(ConnectionState) returning 2.
is equivalent to Get(ConnectionState) returning 2. is equivalent to Get(ConnectionState) returning 3.
is equivalent to Get(ConnectionState) returning 3.
Note:If clients use the IP address of the server rather than the fully qualified host name, they may see an encrypted connection where the SSL certificate for FileMaker Server cannot be verified. To see an encrypted connection with a verified SSL certificate, your clients should add the fully qualified host name as a favorite host in the Launch Center.
Java security considerations
FileMaker Server and FileMaker Cloud require a minimum update of Java Runtime Environment. If that minimum version is not available when FileMaker Server is installed, then the FileMaker Server installer installs the Java Runtime Environment. In FileMaker Cloud, that minimum version of Java is installed when you create your FileMaker Cloud instance.
Security updates to Java are frequently posted to the java.com website. FileMaker Server and FileMaker Cloud updates may include Java updates, but the java.com website provides Java updates more frequently.
The FileMaker Knowledge Base maintains an article called FileMaker Server and Java, which lists the minimum version of Java that you should use with FileMaker Server. Before applying an update to Java on the machine where FileMaker Server is installed, review the information in this article. If you encounter issues after applying an update to Java, remove the update and revert to the minimum version of Java required by FileMaker Server.
PHP security considerations
For Custom Web Publishing with PHP, you must install PHP on the machine where FileMaker Server is located. When you install FileMaker Server, you can choose whether to install the FileMaker supported version of PHP or use your own PHP engine.
Security updates to PHP are frequently posted to the php.net website. FileMaker Server updates may include PHP updates, but the php.net website provides PHP updates more frequently. To apply PHP updates more frequently, install and maintain your own PHP engine.
If you maintain your own PHP engine, you must manually install the FileMaker API for PHP in order to use Custom Web Publishing with PHP. See FileMaker Server Custom Web Publishing Guide.
Note:FileMaker Cloud doesn't support Custom Web Publishing and doesn't use PHP.
Replace the default web server page
FileMaker Server uses a default FileMaker Database Server Website page. This page doesn't reveal any security information about your server, but it does indicate that the server is running FileMaker Server. Clients can view the default page at these URLs:
- http://[host]
- https://[host]
where [host] is the IP address or domain name of the master machine in your FileMaker Server deployment.
To replace this default page, replace the "index.html" file found on the master machine at these locations:
- Windows: [drive]:\Program Files\FileMaker\FileMaker Server\HTTPServer\conf\index.html
- macOS (for HTTP): /Library/FileMaker Server/HTTPServer/htdocs/index.html
- macOS (for HTTPS): /Library/FileMaker Server/HTTPServer/htdocs/httpsRoot/index.html
Other security considerations
Apply updates regularly
Software updates for FileMaker products may contain security improvements. Install updates to keep your FileMaker software as secure as possible. See FileMaker Security Updates in the FileMaker Knowledge Base.
Use strong passwords
The FileMaker platform uses passwords for authentication in several areas. FileMaker Server and FileMaker Cloud require passwords for their administrator accounts. FileMaker Pro allows you to define account passwords and encryption passwords. Use strong passwords. When you are creating a password, FileMaker software analyzes the password and notifies you of the password strength.
For account passwords, you can use external authentication or OAuth identity provider authentication. With external authentication, you manage passwords using Active Directory on Windows or using Open Directory on macOS rather than storing the passwords in FileMaker software. With OAuth identity provider authentication, you manage passwords using supported OAuth identity providers such as Amazon or Google. See Set up external authentication and Set up OAuth identity provider authentication.
Test security settings
When you have completed setting up FileMaker security features, test the security of your solution.
- Set up a test account for each privilege set. Make these accounts active for testing and inactive in your production system.
- Define a checklist of features and functions to test. Step through the checklist with each test account.
- Document your results.
- Repeat testing when new functionality is added.
Continually evaluate your security implementation to make sure your data is still protected. Verify that users have the latest, most secure versions of their operating systems and FileMaker software.
Comply with regulatory requirements
It is your responsibility to fully understand your security compliance requirements and take the appropriate steps.
In addition to the guidelines outlined in this document, depending on your internal or regulatory requirements (COBIT, HIPAA, ISO, PCI, NIST, FIPS, and so on), there may be additional steps you need to take.
- If you need to encrypt all network traffic, turn on SSL in FileMaker Server and then configure SSL for applications and external servers that communicate with FileMaker Server or FileMaker Cloud.
- If you have minimum password standards, use an external authentication server.
- If you need an audit trail, you can build one with FileMaker Pro using tables and scripts. For more complex requirements, consider using a commercially available audit plug-in.
- Windows: Because FileMaker Server depends on Windows for managing SSL, install the latest Windows security updates.
Inform users
Provide documentation on a layout in your solution or on a webpage to explain to users how to securely interact with the solution. Include information about accounts, passwords, how to connect securely to FileMaker Server or FileMaker Cloud, how to use functions and scripts, and any other security concerns or requirements regarding your solution.
Additional resources
Quick reference guide for routine operations
| To | Go to |
|---|---|
| Manage accounts, privileges, extended privileges or file access | FileMaker Pro or FileMaker Pro Advanced: File menu > Manage > Security. |
| Immediately stop someone from accessing any data | FileMaker Server Admin Console:
FileMaker Cloud Admin Console:
FileMaker Pro or FileMaker Pro Advanced:
If the user has access via an external authentication group, remove the user from the external authentication group or disable the user's account in the external authentication server. In an emergency, close the file to prevent access by everyone. |
| Force a user to change his or her password | FileMaker Pro or FileMaker Pro Advanced:
Note:You can also write a script to force more than one user to take this action. If the user has access via external authentication, manage the user's password using your Active Directory or Open Directory server. |
| View log files | FileMaker Server Admin Console: Choose the Log Viewer pane. FileMaker Cloud Admin Console:
|
Types of encryption used by FileMaker
FileMaker encrypts data in different ways depending on how the data is stored or transmitted. This table lists the cipher types used when FileMaker encrypts data.
| Option | Cipher type |
|---|---|
| Account password | One-way hash |
| Admin Console password | One-way hash |
| Database Encryption | AES-256 CBC mode |
SSL/TLS 1.2
|
Note:With SSL, the cipher mode is dependent on the host and client negotiation, so the cipher mode could be CBC or GCM (or others in the future). |
| Secure Storage of container data (with Database Encryption disabled) | AES-128 CBC mode |
| Secure Storage of container data (with Database Encryption enabled) | AES-256 CBC mode |
Ports used by FileMaker Server
See Ports used by FileMaker Server in the FileMaker Knowledge Base.